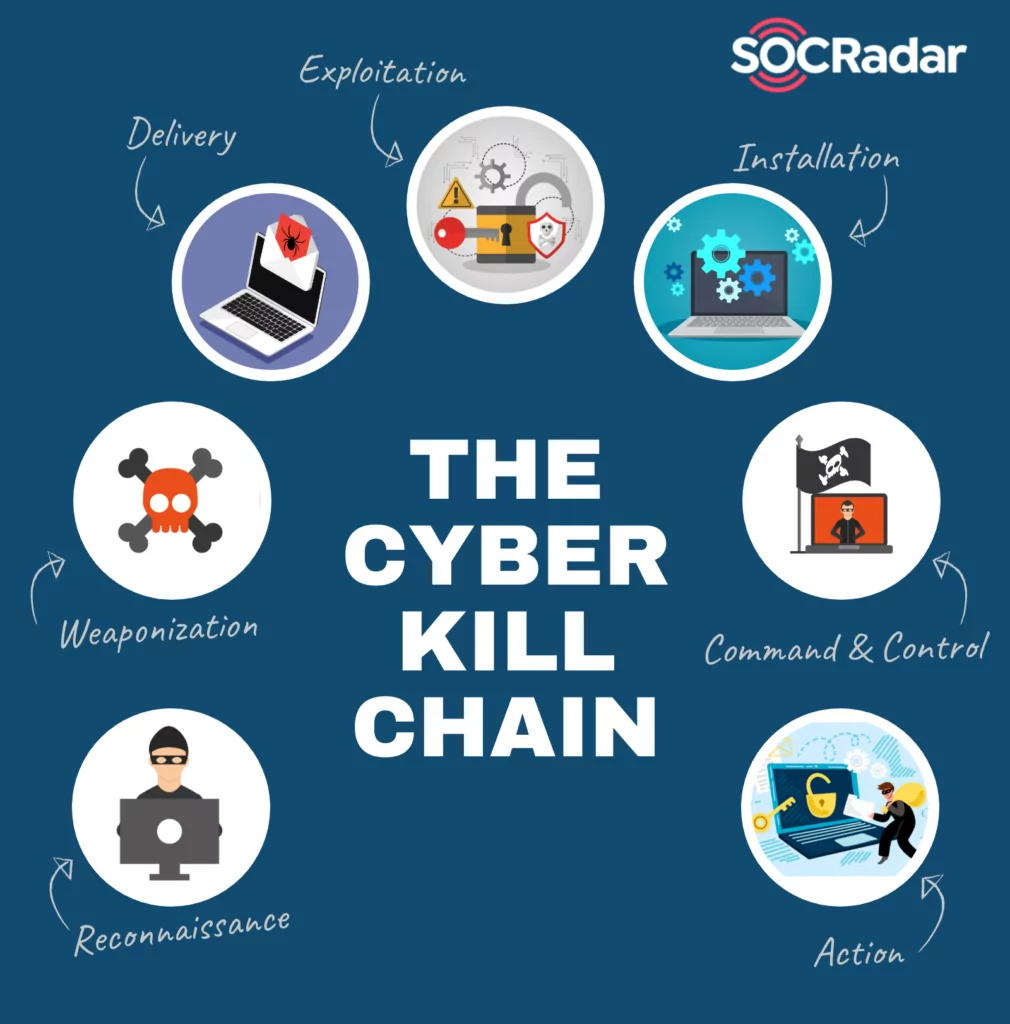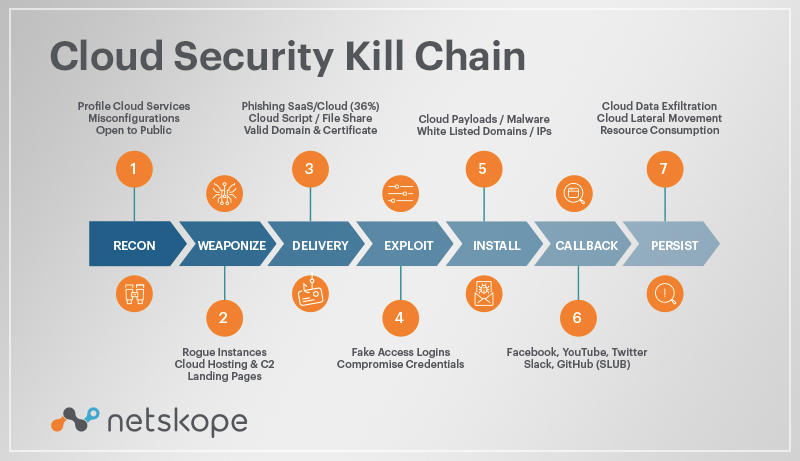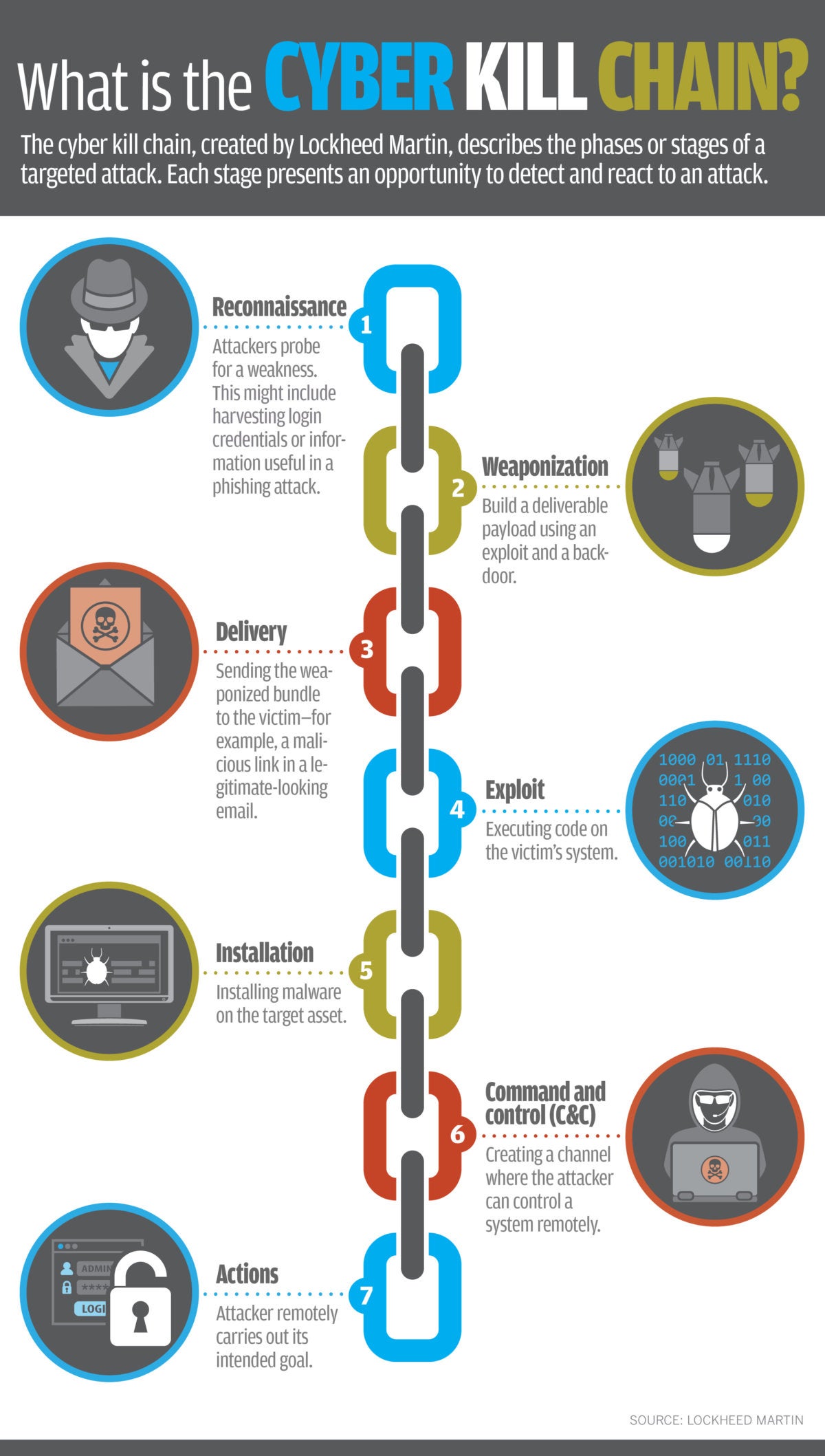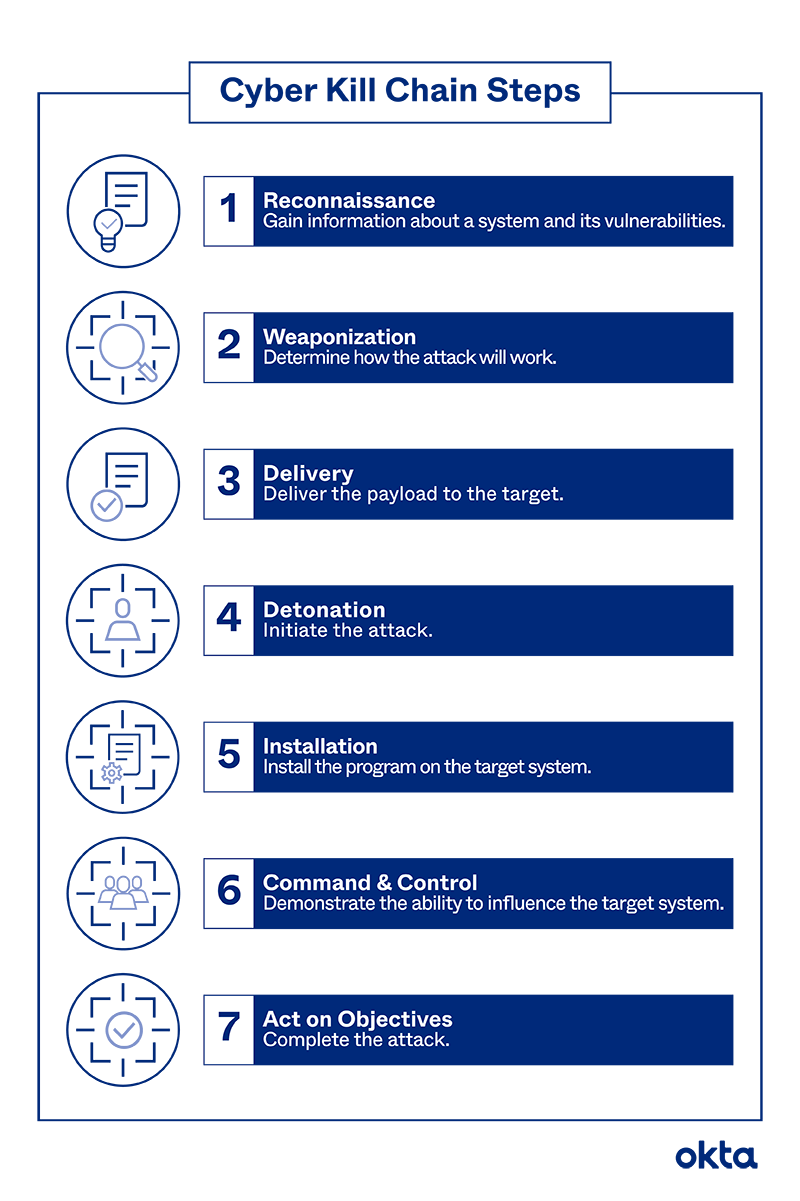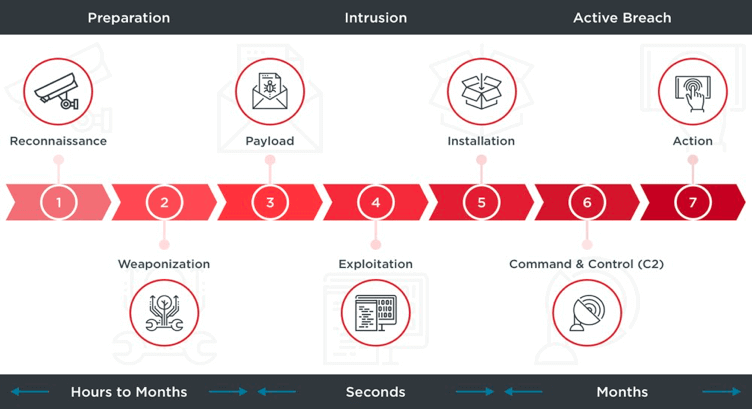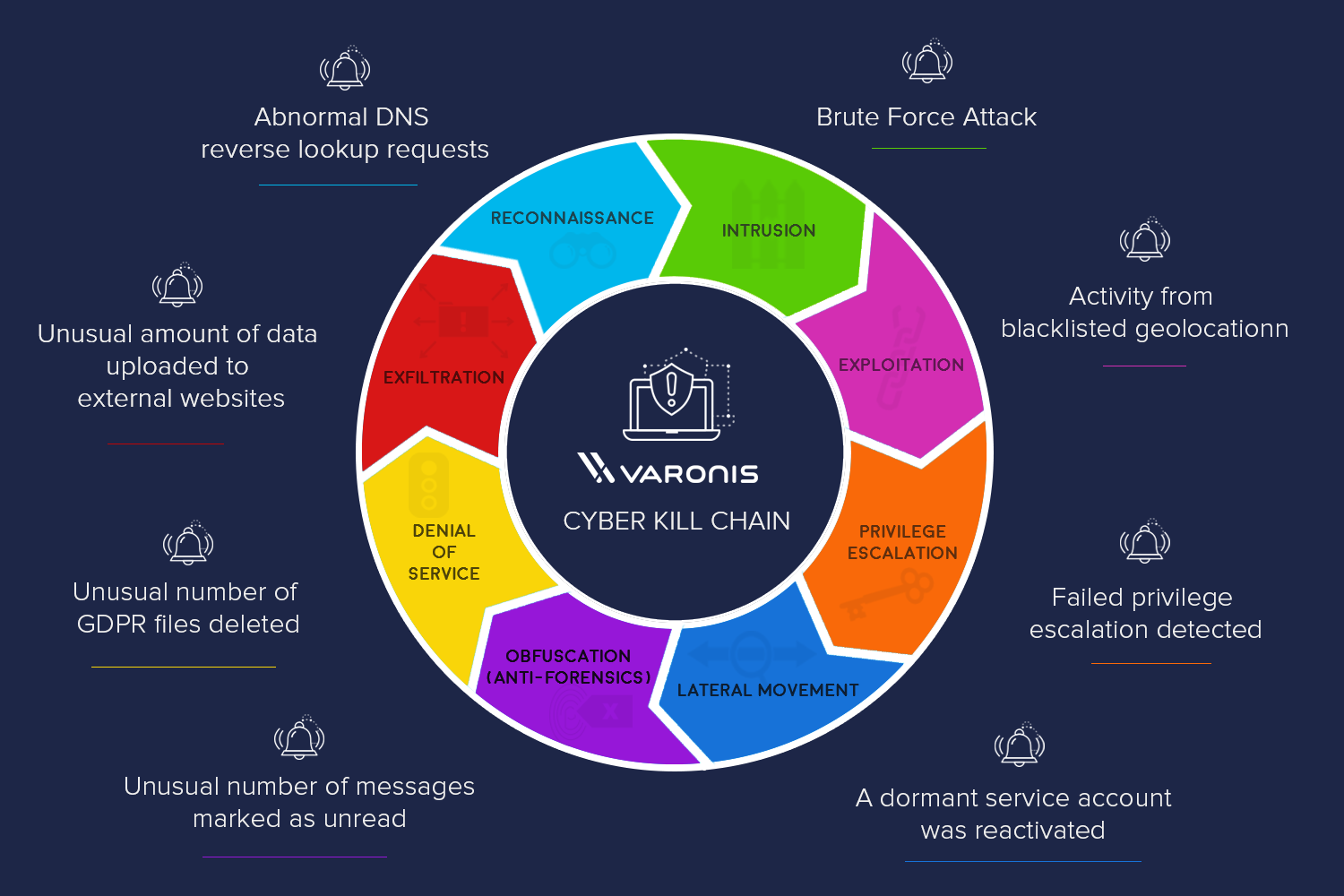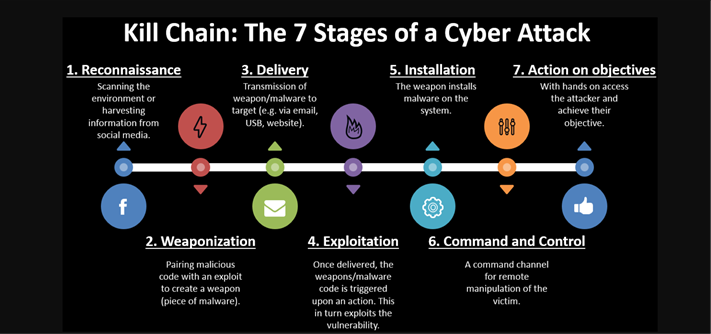
Applied Explanation of the “Cyber Kill Chain” Model as a Cyber Attack Methodology | by Ibrahim Akdağ| Ph.D. | Medium
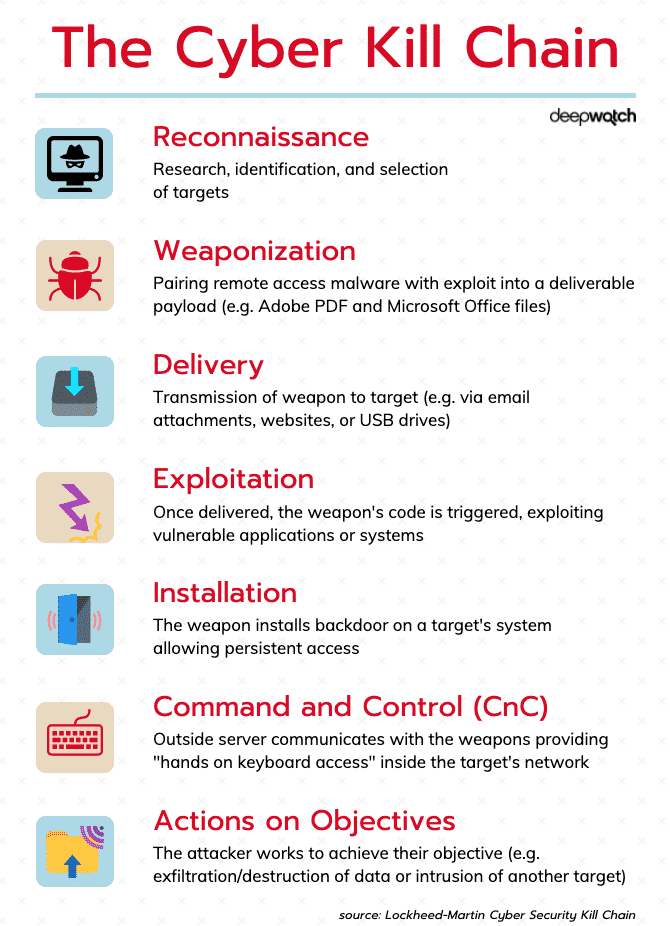
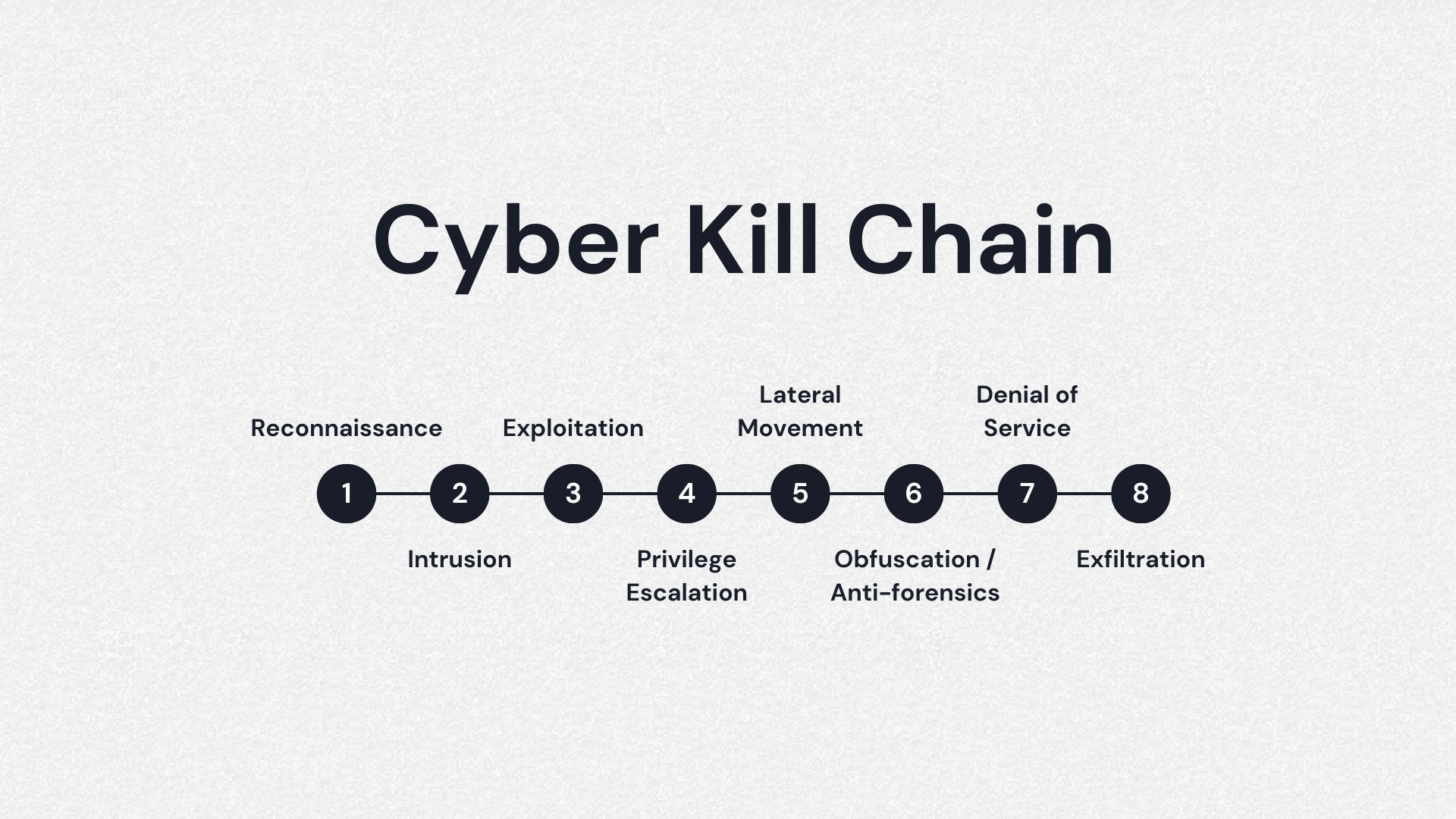
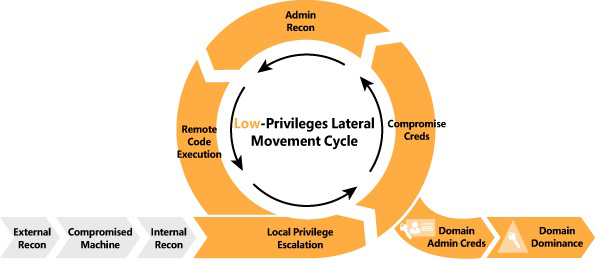
Cyber Kill Chain is a cybersecurity model that discovers the phases of... | Download Scientific Diagram

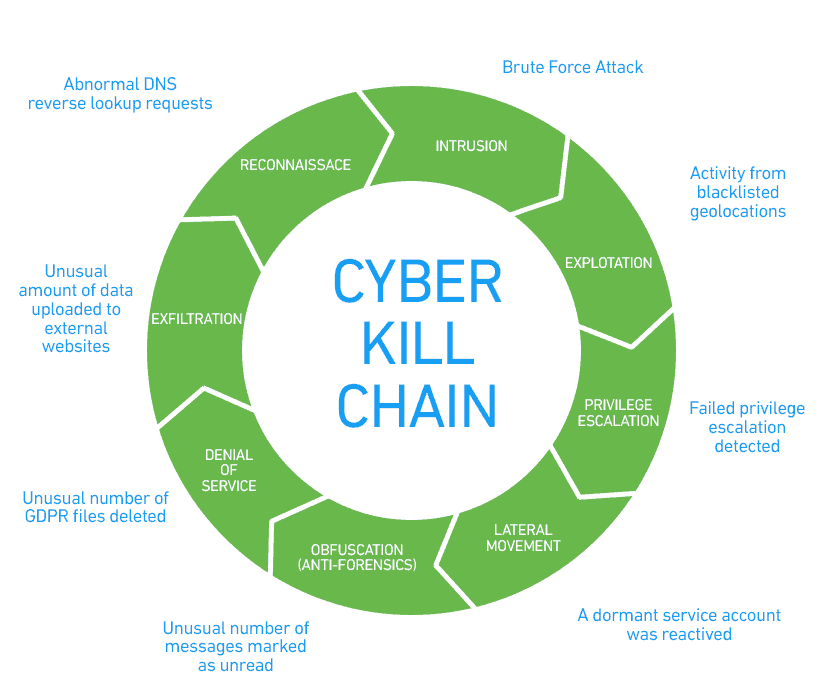
DOD's Utilization of a Cyber Kill Chain Framework to Quantify Cyber Security Investments: Part 3 of the Key Cyber Defense Strategies Series - Government Technology Insider